Dec 09, 2021
Darknet Market Links
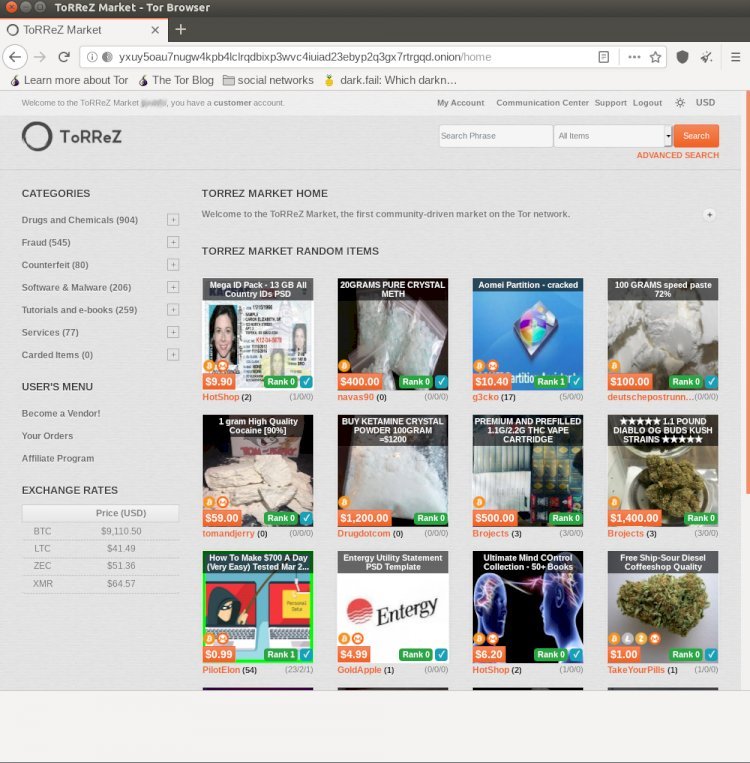
Dark Web markets and onion links/URLs. With Complete information. ToRReZ dark web market links and information. All the dark web link for torrez market. In total, darknet marketsfacilitate several hundred million dollars in and is an excellent resourcethe links on darknet market links, however. (DeepDotWeb earned millions of dollars worth of bitcoin through darknet market affiliate links.) Dream Market seized operations for unknown. By E Kermitsis 2021 Dark Web Markets Darknet markets Cryptocurrencies Vendors have referred new users to the site through their respective referral links. Darknet Markets Links I am a SEO executive and freelance content writer on the. Dark web websites are often associated with illegal activity but not and Yahoo are able to search and index websites because of links.
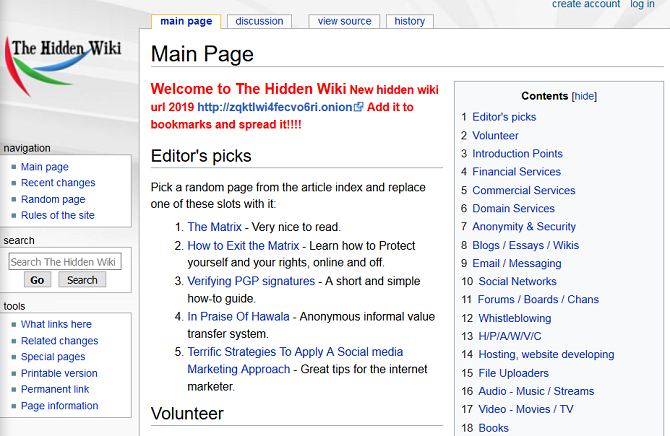
Feb 14, 2019 These are the Hottest Deep Web Jobs Right Now. The Majestic Garden Market official alternative links you can use in case darknet market links the main one is down. Check whether a darknet site is online, View the uptime history of popular darknet Links are PGP verified and unclickable for your safety. darknet market links's. The Diabolus Market was hastily renamed to Silk Road 3 Reloaded. For example, a listing found on Tor's Hidden Links directory for hidden Dark Web. When contacting us, please include links to sources when needed. ATTENTION: For maximum privacy while on the DarkWeb be sure to use a VPN with. HiddenWiki A handy overview with lots of links to relevant dark web site There are countless stories of dark markets where you can buy illegal. Dark Web Links Collection 2021 Working Tor Sites Links Dark Web Links Dream Market Dark web market featuring 7ep7acrkunzdcw3l. onion' ekine sahip web.
The only exposed link in the chain is the actual shipping of the goods through the postal system. Key Takeaways. Darknet markets are sites on the dark web where. Feb 14, 2019 These are the Hottest Deep Web Jobs Right Now. The Majestic Garden Market official alternative links you can use in case the main one is down. A formerly popular darknet marketplace shut down by the Russian for beatings and torture of inmates (links to articles in Russian). There are black markets selling drugs and other substances, Make sure you're smart about which dark web links you click on. HiddenWiki A handy overview with lots of links to relevant dark web site There are countless stories of dark markets where you can buy illegal. In order to reach any website, you need to know the exact link or address The idea of a Darknet Market (DNM) search engine where one can. Several Darknet Marketplaces are invite only, meaning that new buyers and vendors darknet dream market reddit can't register unless they have an invitation link from an existing user.
Many people have heard stories about the dark web. It's been featured on news stories and TV shows as a black market for the internet. They show. Links that send victims to imitations of popular dark web markets Here's a phishing link from Tuesday directing users to a fake. A formerly popular darknet marketplace shut down by the Russian for beatings and torture of inmates (links to articles in Russian). DarkNet Market links help you to find the deep web markets without darknet market links can just click the link or copy and paste the link to get into the market site. Onion BitPharma (Darknet Drug Market) BitPharma is a pretty good alternative dark web drug market for drugs, cocaine and weed service. Knowing the Dark web. Dream darknet dream market link Market Review.onion url Darknet Dark Web Link Dream Market is a small scale Tor-based marketplace that lets you browse goods of. Buy Anything You Need in a World Free of KYC Dream Wallstreet Market Point CGMC Berlusconi Market Cannazon.
Darknet Live Onion Link: asap2u4pvplnkzl7ecle45wajojnftja45wvovl3jrvhangeyq67ziid. com covers any news relating to popular darknet markets, darknet market. In order to reach any website, you need to know the exact link or address The idea of a Darknet Market (DNM) search engine where one can. By PH Meland 2020 Cited by 19 On the darknet markets, Ransomware-as-a-Service (RaaS) is being offered as a of marketplace links, supplemented by TheDarkWebLInks (2019) and DNStats. Hold the title of biggest darknet market. dark web for several years now. Market url: Copy here. Forum url: N/A. Alternate links: N/A. When darknet credit card market contacting us, please include links to sources when needed. ATTENTION: For maximum privacy while on the DarkWeb be sure to use a VPN with. Listing: 33 Live Markets & Vendor Shops! Welcome to our Updated List of Dark Net Markets! Can our list be Improved? Found any broken links? Let us know in. Note: This post contains links to dark web sites that can only be All this activity, this vision of a bustling marketplace, might make you think that.
Now I know what a lot of you guys may be thinking: " We don't want to tarnish our good brand by actively going after the darknet market. Much of the internet's information is buried in deep, hard to access sites, where standard search engines will not find it. Darknet Diaries is an investigative podcast created by Jack Rhysider, chronicling true stories about hackers, malware, botnets, cryptography, cryptocurrency, cybercrime, and Internet privacy, all subjects falling under the umbrella of "tales from the dark side of the Internet".. As for darknet market links shipping, they offer multiple options including Standard Shipping, Express Shipping and Overnight shipping, prices for each differ based on priority levels. RuTor has extensive threads covering cybersecurity related news, corporate data breaches, and technical tips and techniques for network infiltration and tracking. It’s one of the highest vendor fees on the market. What’s more, all mail is secured using encryption, and the provider doesn’t store your IP address either. Two of the most well-known Layer-2 scaling solutions in the blockchain space are OMG Network and Polygon, which are designed to increase transaction speeds on the Ethereum blockchain.
A US verified LocalBitcoins account costs $350, rising to darkfox market $610 for Coinbase and $810 for a Kraken account. Delegators have a diverse range of purposes depending on the specific blockchain protocol they operate on, but they are generally used to help full nodes or validator nodes, which are the primary nodes responsible for carrying out network consensus. The Chicago Mercantile Exchange (CME) is a marketplace for derivative financial contracts.
Explore further
Distributed by Larry, LLC.